The Anatomy of a Digital Shakedown: $70,000 in Coordinated Racketeering | Project: Bullyish by Lillee Jean Trueman
- Mar 20
- 9 min read

The more crime that is committed, the more I document and educate. In my latest analysis for Project: Bullyish, we're continuing to explore the "Nexus" strategy. From digital deepfake explicit forgeries, to the clear weaponization of the American legal system, with sealed court records for commercial gain...I now want to touch on the subject of computer fraud.
Before continuing on, I'd like to refresh the truthful objective here: I am documenting a Multi-Scale Digital Racketeering operation, with provided, redacted proof of a funded, high-tech siege. Based on my analysis of server logs and industry-standard cloud pricing from October 2025 to March 2026, I have formulated my own forensic assumption and estimate that this campaign has cost upwards of $70,000+, but in my honest opinion, nearing $100,000 upwards.
The evidence is truly undeniable, with real consequences. Below, you will be looking at a multi-layered, high-cost global infrastructure siege. I'll explain robots.txt, TCP three-way handshake, as you read along, but it's vital to understand that this isn't just a "troll" at a desk; this is a coordinated operation utilizing expensive, enterprise-grade nexuses to target my archives.
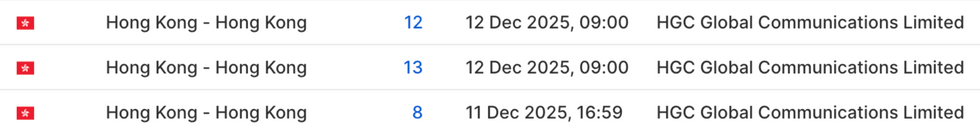
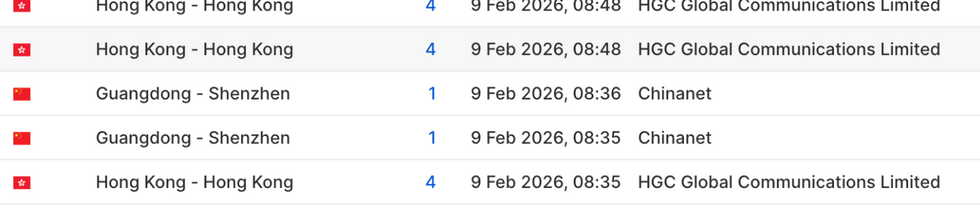
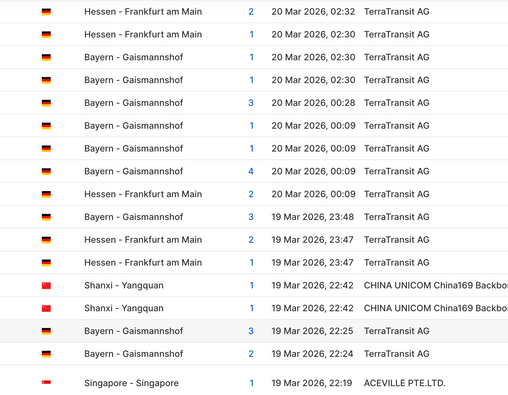
When you look at the forensic data, you see the "Main Node" isn't just using one tool...they are orchestrating a literal cloud siege across three continents simultaneously. Not only is this stressful, but it's also being used to conduct coordinated surveillance on my family. Let that sink it. PLEASE NOTE, despite these being server networks operating from the same I.P. ranges (thus proving DDOS further, and bad faith), I will not be showing their ranges, just the volume of attacks, and the provided forensic proof of the ISP provider. Otherwise, all personally identifying information (despite once again these being the personally identifying information of BOTNETS for distributed attacks are fully redacted with only date, country, attempts, and internet provider shown) for good faith, educational purposes.
The "Why": The Profit of Suppression
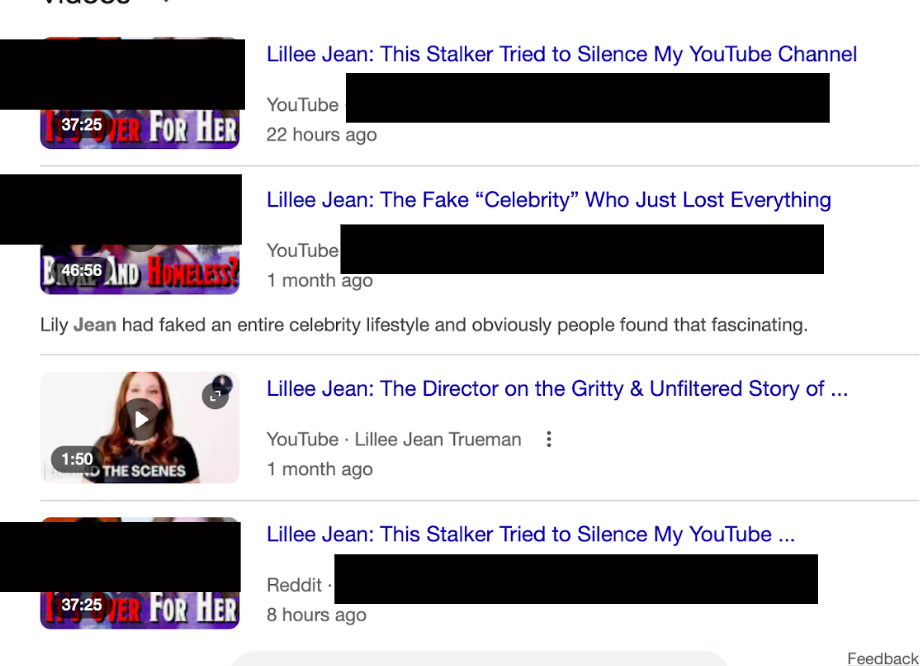
To understand any of this, you have to understand why "takedown Lillee Jean", as this syndicate calls it. This ecosystem creates a profit from suppression, and commercializes me...without any consent.
The goal is to de-rank and replace, ultimately feeding a greed of the heart (the client's goal) and literal greed (the people the client pays to produce, who depend on the client's next job offer). I suggest reading my hate-for-profit article, which elaborates more on the subject.
By flooding my site(s) (this occurs on all my official domains) with "Distributed Denial of Service" (DDOS) attacks from clusters such as China Unicom and Tencent, they attempt to slow or crash my official archive. Through probing and high-speed site breaches, this causes stress on a server. Google crawls a site, sees it's slow, and over time can de-rank. This causes the planted bad actor "creations" to rank number 1, while the official site becomes less than the first page, almost like I do not exist. This is, anyway, a violation of the Right to Publicity act, and the ability to fairly compete within your own name (FTC). It's worth mentioning, in synergy, my domains are being doused with link farms utilizing highly explicit terms, around the same dates of these DDOS attacks. As of January 2026, I filed a new NYPD report on new amounts of deepfakes, which were nonconsensual - there is no coincidence. Put two and two together. So if one way doesn't work, the "client" attempts poising (you get penalized for bad referrals, in simple terms, by Google).
Back on topic, while a site is under stress, "Success" nodes (such as Aceville and TerraTransit) scrape every production log, image, audio/visual, and some nodes even harvest sealed court documents to feed a false narrative (the NY court system was breached, with sealed documents exposed to CHAN boards). Wherever the client wants, they go. Just pay up.
It's vital to note that this is documented to begin with TENCENT, BAIDU, then ACEVILLE, and ACEVILLE II occur. Aceville PTE. LTD, a Singapore-based investment holding company, and, a subsidiary of Tencent. It's used for investments.
Deconstructing the Infrastructure: Spoofing and Stealth
I have shown only a small redacted sample, as with all my work, I still uphold my own integrity.
The data reveals a calculated transition between providers, proving that when one "front" is blocked, the syndicate simply probes and migrates to a more expensive, industrial-strength layer. My logs show they are using Headless Chrome, Opera, Phoenix Browser, and spoofed User-Agents (some spoofed agents of Chrome not available yet) to mimic human behavior. They attempt to mask their automated nature by rotating through several "browser" identities, such as Chrome, DuckDuckGo, and Opera, but their infrastructure remains fixed on the same backend data centers.
Despite my robots.txt, which is a "No Trespassing" directive to crawlers, that clearly defines off-limit zones (can be respected and upheld in court), this syndicate continues to bypass my legal boundaries. Many scrapers abide by robots.txt files, but black-hat ones often do not, forcing victims to be impacted, with their privacy, dignity, and upkeep tarnished. It's a coward's way to cheat an outcome.
Every success hit that occurs after a "Disallow" instruction is documented evidence of Computer Trespass, and prosecutable; it's a crime. This persistent disregard for standard directives proves that this isn't an accidental crawl, but an intentional, criminal breach designed to harvest data for the production of non-consensual deepfakes and identity theft.
I’ve kept the NYPD updated, continue to file FBI IC3 reports, and have kept documenting a strategic infrastructure migration I'm seeing, through the layers of TerraTransit AG in Germany and massive TCP/DDoS assaults from AWS nodes, as well as Azure nodes in Virginia, reaching over 1,000's of attempts an hour to overwhelm my servers (I filed an ethics report to Microsoft).
A very vital point, even after Tencent acknowledged my abuse reports and claimed the harvested material was deleted (I submitted a standard IP abuse report, in TCP format...not a DMCA. TCP shows how an IP connects to a server, fully, in very simple terms), the "client" simply pivoted with Tencent, using a global proxy network in Hong Kong and the Philippines to hide their location and restart the cycle of scraping my 2015-2026 archives for AI-generated deepfakes and SEO sabotage.
The recent pivot to Alibaba infrastructure, as shown above, the last redacted screen capture, completes the weaponization of the BAT trinity (Baidu, Alibaba, Tencent), the three dominant Chinese tech conglomerates. This demonstrates a coordinated use of global enterprise power to bypass regional blocks and sustain this criminal aggravated harassment. All information they scrape, ends up within weeks on sensationalized publicly traded platforms for pure profit. Take that with the client's profit (of the heart), and the person working as an agent for the client (they just paid a bill off this narrative). This is coordinated.
The Results of Data Scraping
Since October, the "client" behind this infrastructure has produced 6+ mid-tier videos designed specifically for identity theft, character assassination, coordinated aggravated harassment, and a dehumanization of myself and my family. These are the literal end products of the data harvested by the Aceville and China Unicom clusters.
During the period of publishing, scraping becomes probes, and slows.
Within just a few weeks of these "Success" scrapes, we have seen a surge in: The creation of explicit, synthetic forgeries used to erase my natural born rights of consent and attack my dignity (show above); A coordinated rollout of impersonating profiles (mainly explicit) designed to splinter my identity and mislead the public; and lastly a direct correlation between these AI-generated photos and a spike in explicit, derogatory search queries for my name, a truly calculated move to poison my SEO.
The Forensic Bill: A $70,000+ Projection
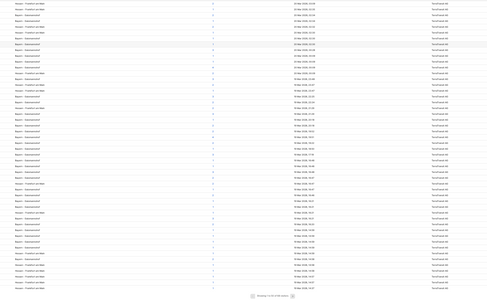
This is truly an opinion due to the available rates. The following is a professional estimate based on current enterprise rates for high-bandwidth servers, managed botnet services, and AI API consumption during the six-month window of October 2025 to March 2026.
Infrastructure Component | Estimated Monthly Cost | 6-Month Total (Est.) |
Global Infrastructure (Tencent/Aceville/China Unicom) | $3,500 | $21,000 |
Proxy Rotation & Stealth (TerraTransit/M247/Vultr) | $2,500 | $15,000 |
AI Processing & Scripting (ChatGPT/Grok Enterprise) | $1,500 | $9,000 |
Coordinated Labor (Management of the "Nexus") | $5,000 | $30,000 |
TOTAL ESTIMATED EXPENDITURE | $12,500 | $75,000+ |
The Accelerated Cycle of Digital Assault (Oct 2025 – March 2026)
The forensic evidence above, is redacted; however, captured in these logs is a persistent pattern of Computer Trespass. Despite explicit directives in my robots.txt file this syndicate continues to probe archived and protected pages, such as "Lillee Jean Talks Live", and versions of my site that have not existed since 2016, forming ghost strings, in which, could trigger Google to crawl such pages (and has happened), which hurts ranking.
The data shows hundreds of unauthorized attempts from industrial clusters to probe, scrape, and ultimately overwhelm server defenses. By intentionally bypassing these digital "No Trespassing" signs through spoofed User-Agents and Headless Chrome, these bad actors are in direct violation of the Computer Fraud and Abuse Act (CFAA), which actually criminalizes exceeding authorized access to a protected system.
These logs don't just show "traffic". They provide a chain of custody for a funded, six-figure racketeering operation designed to harvest my intellectual property for criminal exploitation, and pure commercial profit.
With sponsors near my face, AdSense revenue flowing, and underground profit, I wanted to share this today, so that any other person going through this understands, you have rights, these are criminals, and here is how this all applies. I also wanted to share steps I have taken to protect my privacy, and rights, such as filing ethics reports, when criminal action occurs, and taking that to the NYPD with forensic proof. I feel many victims feel helpless, and the truth is, that's the eco-system these bad actors WANT you to feel trapped in, so they can keep you "down".
Racketeering and Federal Reporting Angle
Under the RICO (Racketeer Influenced and Corrupt Organizations) Act, racketeering involves a "pattern of illegal activity" carried out as part of an enterprise. Amazon AWS and Microsoft have been cooperative with law enforcement, as with each report, I just give them the detective's contact, so they can have verifiable proof of bad faith on their client's end.
In my case, when a "client" hires a Black Hat agency to systematically sabotage a Director’s business and livelihood, and I have sustained aggravated harassment/stalking active police reports, with additional reports for explicit deepfake imagery distributed of me, with this coordinated criminal activity spanning around 10 years, they are engaging in a racket. Formulating the "chaos" so they can control the narrative and results, and generate the profit.
A server log doesn't lie. When you see thousands of hits from servers and clusters hitting a single human for months, with sustained downtime, forget 'regular crawling traffic' - you are looking at a funded criminal enterprise. You can spend $70,000+ to try to bury the truth, but it's simply a fingerprint. This isn't an opinion. It’s a crime that was committed against my family.
I have officially reported these logs and the associated infrastructure to the FBI's Internet Crime Complaint Center (IC3) and the NYPD Cyber Crimes Unit.
What I've shown is a miniature of the full picture, but enough to hopefully help others out there.
Lillee Jean Trueman
Please visit the official Site:
Forensic Methodology and Estimations: The financial figures, expenditure projections, and infrastructure valuations presented in this report (specifically the "Forensic Bill" and "Total Estimated Expenditure") are forensic estimates formulated by the author. These projections are based on a comparative analysis of industry-standard market rates for enterprise-level cloud egress, global proxy rotation, high-compute data center bandwidth, and AI API consumption during the period of October 2025 – March 2026. Because the private invoices and internal service agreements of the identified third-party infrastructure providers are not public record, these figures represent a good-faith expert projection based on the documented volume and frequency of server logs. No Malice / Investigative Intent: This article is a work of investigative journalism and forensic study published as part of Project: Bullyish. The purpose of this publication is to document patterns of cyber-harassment, educate the public on digital safety, and provide a transparency report regarding the security of the author’s intellectual property. Any mention of specific entities or service providers (e.g., Tencent, Alibaba, Microsoft) is based on direct forensic evidence captured in server logs (IP addresses and User-Agents) and is intended to describe the technical path of the traffic, not to imply that the parent infrastructure providers are intentionally complicit in the harassment. Legal Characterization: Terms such as "Racketeering," "Computer Trespass," and "Digital Shakedown" are used in a descriptive and investigative context to characterize the pattern of conduct observed in the forensic data. These characterizations are the opinion of the author based on the documented "course of conduct" and are not intended to serve as a legal determination of guilt, which is the sole province of a court of law. Reporting and Evidence: All original, unredacted logs, timestamped data, and TCP handshake records referenced in this study have been preserved and submitted to the FBI’s Internet Crime Complaint Center (IC3) and the NYPD Cyber Crimes Unit as part of an active, ongoing criminal investigation.
© 2026 Lillee Jean Trueman. All rights reserved.